Browse the categories
Data Science & Business Analytics ( 12 )
View All
Why Data Analysts Are in High Demand in the UK
Transforming UK Industries with Powerful Insights
Insights and Trends in the UK Industry
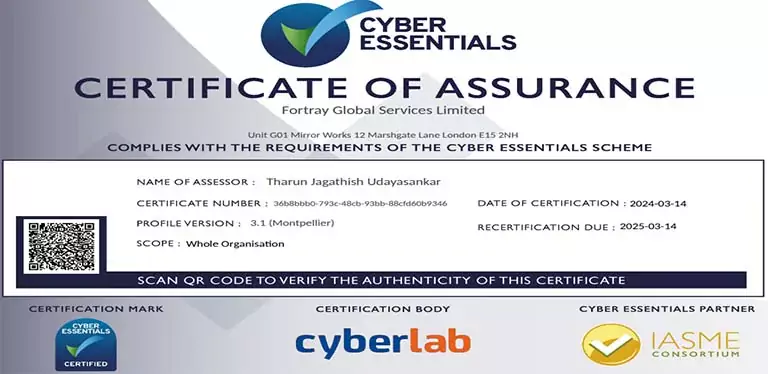
Cyber Security ( 13 )
View All
Why Small Businesses Are Prime Targets for Cyber Attacks
How much do cyber security jobs pay in London?

Is Cybersecurity a Good Career in the UK?
Cloud Computing ( 7 )
View All
What is the salary of a cloud infrastructure engineer?

Is Cloud Infrastructure Engineering a Good Career?

Is Cloud Computing in Demand in the UK?
Project Management ( 1 )
View All
The 5 Most Effective Project Management Methodologies for Students and Professionals in the UK
Guides and Insights ( 16 )
View All
Insights and Data for a Successful Transition

Cyber Staffing Shortages Remain CISOs' Biggest Challenge in 2025

What Skills Do I Need to Become a Data Scientist?
Digital Operation ( 4 )
View All
Why Digital Marketing Is a Must-Have Skill in 2025

The Real Impact of Social Media

What is Quality Control?
Our most read articles
Build a solid portfolio to showcase your skills to tech recruiters
Create various web and AI apps, culminating in a live demo to a real audience. Enhance your profile with a portfolio ready for interviews.

Unleashing the Potential of Cloud Services for Learning
and Growth
With the introduction of cloud computing, the digital world has undergone a paradigm shift

Mastering Cloud Security: A Complete Guide to Protecting
Your Data in the Cloud
In today's digital landscape, the adoption of cloud computing has revolutionized

Maximizing Cloud Security: A Comprehensive Guide
Discover the importance of cloud security and learn essential strategies,

The Ultimate Guide to Penetration Testing
Penetration testing, often referred to as pen testing, is a critical

The Ultimate Guide to Ethical Hacking
Welcome to the Ultimate Guide to Ethical Hacking: How to Safeguard